Kali Linux team emphasizes on a major visual changes to their 20xx.1 release, that is the first release of every year. And Kali Linux 2022.1 release brings in new visual refresh and a new flavor known as offline ISO.
There are several other improvements with Linux Kernel upgrade, some new hacking tools, live VM support, Apple M1 support, and more. Let us look at the major highlights for Kali Linux 2022.1.
Kali Linux features like drag ‘n’ drop, copy/paste have now been enabled by default to give users a better experience in a VM with i3.
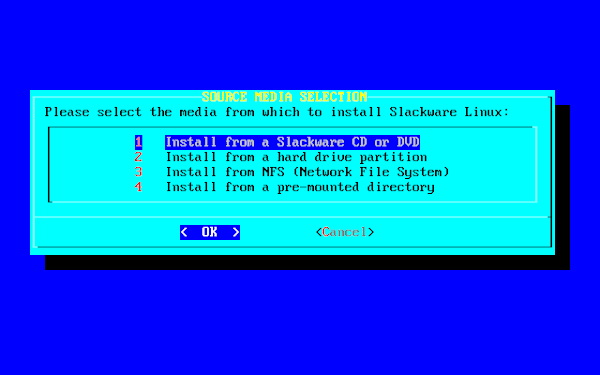
And the new flavor, that comes as a standalone offline ISO includes everything from “kali-linux-everything” packages, offering you the ability to download an offline ISO without needing the packages installation separately.
Kali Linux 2022.1 brings new tools with some worthy of them highlighted below:
Also, there are tweaks to remove the exit code, skull icon, and number of background processes, with significant improvements for desktop and Raspberry Pi.
For existing users of Kali Linux, a quick update can be performed using the following commands:
And for new users, its ISO is available in the official site for download, but note that ‘Everything’ flavor is available only via Torrents.
There are several other improvements with Linux Kernel upgrade, some new hacking tools, live VM support, Apple M1 support, and more. Let us look at the major highlights for Kali Linux 2022.1.
What's new in Kali Linux 2022.1 Release?
Kali Linux features like drag ‘n’ drop, copy/paste have now been enabled by default to give users a better experience in a VM with i3.
And the new flavor, that comes as a standalone offline ISO includes everything from “kali-linux-everything” packages, offering you the ability to download an offline ISO without needing the packages installation separately.
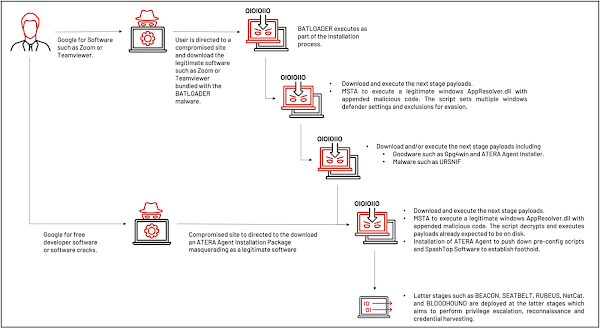
Kali Linux 2022.1 brings new tools with some worthy of them highlighted below:
- New packages for ARM64 architecture including feroxbuster
- Enable legacy algorithms, ciphers, SSH using a setting in kali-tweaks
- Accessibility improvements for speech synthesis in the Kali Linux
- Introduction of some new tools like email2phonenumber, dnsx, naabu, and proxify
Also, there are tweaks to remove the exit code, skull icon, and number of background processes, with significant improvements for desktop and Raspberry Pi.
How to Download and Install Kali Linux 2022.1 Release?
For existing users of Kali Linux, a quick update can be performed using the following commands:
echo "deb http://http.kali.org/kali kali-rolling main non-free contrib" | sudo tee /etc/apt/sources.list sudo apt update && sudo apt -y full-upgrade cp -rbi /etc/skel/. ~ [ -f /var/run/reboot-required ] && sudo reboot -f
And for new users, its ISO is available in the official site for download, but note that ‘Everything’ flavor is available only via Torrents.