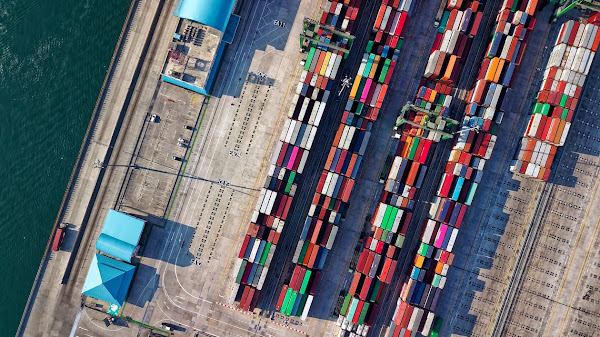
The first Tesla Semi trucks were delivered to customers on Thursday at a ceremony at the company's Gigafactory in Sparks, Nevada, five years after their initial unveiling. The trucks' 2019 production launch was postponed for a number of reasons, including the COVID-19 pandemic and a global parts shortage. The trucks were first revealed in concept form back in 2017. PepsiCo representatives were present to accept the initial shipment of trucks after placing a reservation for 100 Semis soon after its announcement.
When towing an 82,000-pound (37,000-kg) load, Musk claims that the Semi truck has a range of 500 miles (roughly 800 kilometers) on a single charge. It can carry more than 33,000 pounds (14,969 kilograms) of cargo due to its weight restriction. According to the CEO of Tesla, the truck has three times the power of a diesel-powered truck. It's a "game changer," he said. Several automakers, including Daimler, Volvo, and China's BYD, unveiled their own trucks in the time between Semi's announcement and unveiling.
The Semi is being promoted by Tesla as the truck of the future. However, while the company has had difficulty launching production, EVs have already been accepted by the rest of the trucking industry. Major machinery producers like Daimler, Volvo, Peterbilt, and BYD have been developing their own electric long-haul vehicles. According to Bloomberg, the three Tesla Semis that were delivered today were the last component of a $30.8 million project that was financed in part by the California Air Resource Board. Even Nikola Motors, which has battled accusations of fraud and executive turnover, delivered a truck powered by hydrogen before Tesla.
Tesla is a favorite among many car enthusiasts thanks to its sleek, futuristic designs. But there are other elements that influence how popular electric cars become. For environmental reasons, many nations are enacting legislation to phase out trucks powered by internal combustion engines. Tesla has not yet disclosed the Semi's cost. Generally speaking, electric trucks are more expensive than their diesel-powered counterparts by about 70%. In the long run, though, they are significantly more cost-effective due to fuel and maintenance savings.














.png)
.png)